How A2SPA Protects Your Agents
A2SPA addresses the critical "Payload Trust Gap" - where all upstream security layers assume incoming payloads are legitimate without verification.
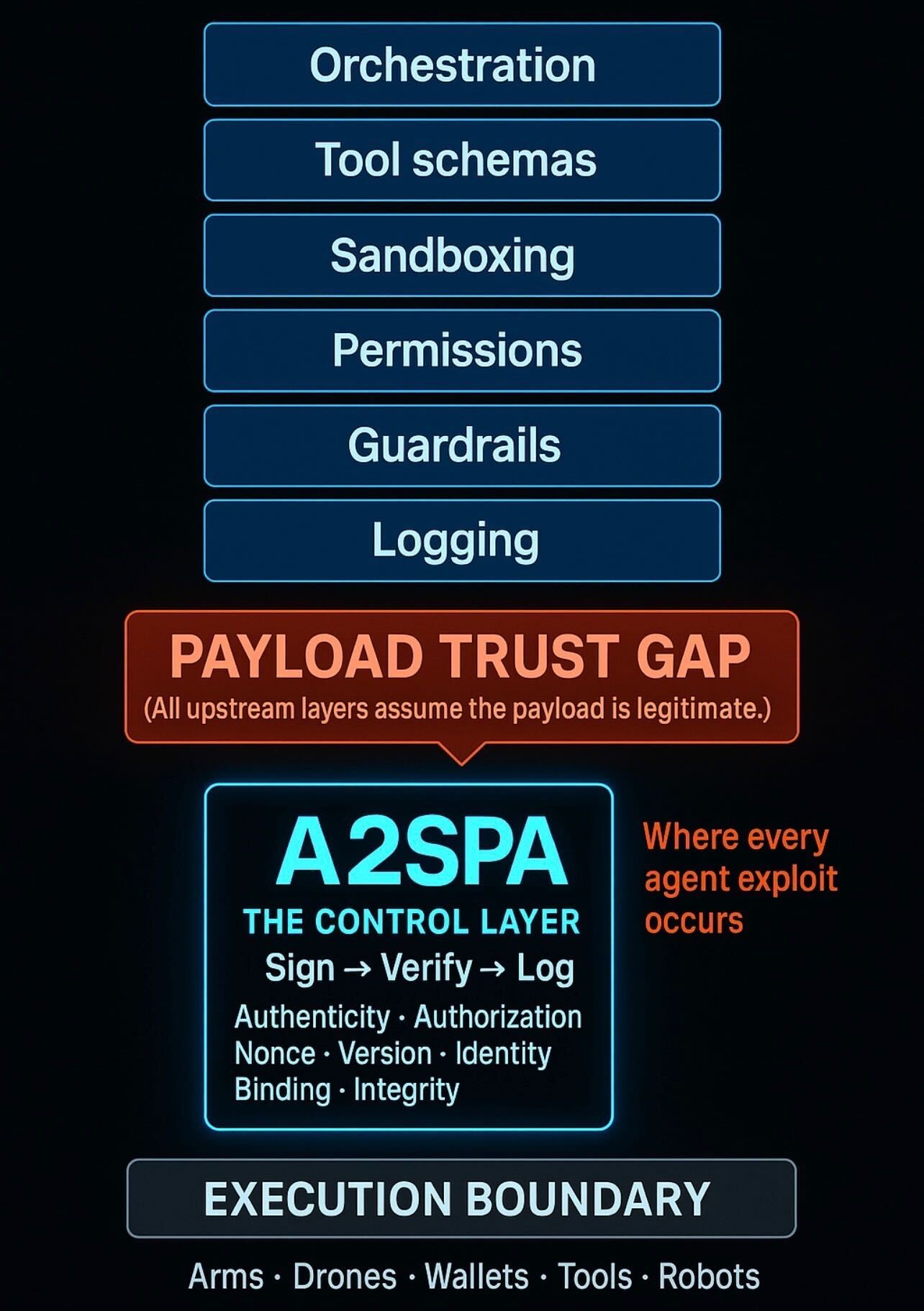
The A2SPA Control Layer sits at the execution boundary, providing cryptographic verification before any agent action is executed. This ensures Authenticity, Authorization, Non-repudiation, Integrity, Identity Binding, and Version Control.
Without A2SPA, orchestration layers, tool schemas, sandboxing, permissions, guardrails, and logging all operate on the assumption that payloads are legitimate - creating the vulnerability that enables every agent exploit.